In my previous posts, I discussed how Platform as a Service (PaaS) might be a suitable platform for individual developers and enterprises alike to innovate, develop new applications and run their applications. I also discussed on how it provides them with a runtime environment to migrate their existing applications to the Cloud.
In this post, Cloud Migration Strategy, I will discuss various factors that may impact the CxOs’ decisions for adopting Cloud computing and their Cloud migration strategy. I will also be discussing the factors impacting IT when migrating existing applications to the Cloud.
Cloud Migration Strategy
Based on Gartner’s report released on January 21, 2011, the CxOs top business priorities were increasing enterprise growth and reducing enterprise costs. Their top technology priorities were Cloud computing, Mobile technologies, and IT management.
It is apparent from the report that CxOs understand that Cloud computing is one of their corner stones to achieve their business goals and they understand that Cloud maybe the path to the future. However, they are still resisting the transition and continuously evaluating the risks associated with their Cloud migration strategy.
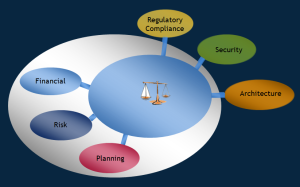
Figure 1 lists most of their concerns that are centered around regulatory & compliance, security, architecture, planning, risk and financials.
Regulatory Compliance: There are a number of regulations that organizations have to adhere to. Regulations such as SOX, GLBA, FISMA, PCI-DSS and others. Different regulations apply to different industries and through strategic bench-marking and various compliance frameworks, CxOs can assess their risk associated with these regulations for making their strategic decision to move to the Cloud.
Security & Privacy: On one hand, CxOs may consider cost, flexibility and speed as drivers for adopting the Cloud. On the other hand, Corporate IT sees security & privacy as their biggest inhibitors to make their move to the Cloud. With the advent of the Cloud, the delineation of responsibilities between Corporate IT security and Cloud providers became fuzzy. The security of the infrastructure is moved to the Cloud providers and its robustness is beyond the Corporate IT control. Besides the infrastructure security, corporate IT has to consider other security factors such as audit, control and monitoring. Corporate IT also has to address application security, identity and access management, data encryption, transmission, data separation and data location. It also has to address the processing of sensitive, regulated and classified data and ensure they are compliant with various IT governance and privacy frameworks such as ISO 9001, 27001, 27002, ITILv3, CMMI, CObIT, NIST 800-53 controls and FISMA.
[AdSense-C]
Architecture: There are two main aspects related to architecture: 1) Enterprise Architecture and 2) Application Architecture.
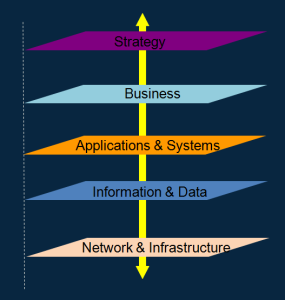
Enterprise Architecture: It is at the heart of the Cloud migration strategy as it provides an enterprise-wide view of the interactions of the five key domains: strategy, business, information, systems, and technology as depicted in the figure 2. It provides IT an opportunity to have an accurate inventory of their servers, applications, required licenses and middleware currently running in their data centers.
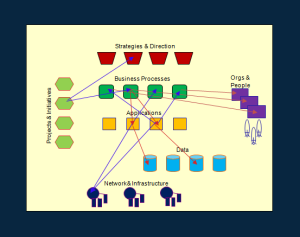
By mapping the relationships of the applications across the five domains as shown in figure 3, IT will be able to get answers for the following questions:
- What is the potential business impact by modifying or migrating the applications?
- How are the projects aligned with the strategy?
- Who is responsible for which business functions?
- Which business processes depend on what applications?
- What applications depend on what data and technologies?
The answers to these questions provide IT a clearer view about the business as a whole. When IT is formulating their Cloud migration strategy, this information allows them to take into account the critical business processes and the corresponding applications that will impact them during the migration process. IT can assess the operational impact on the business and which applications will require the most effort, resources and funding to migration.
Application Architecture: This post only focuses on the Cloud migration strategy of existing applications.
Corporations have modern and legacy applications running in their data centers. Corporate IT have a task at hand to make decisions on whether or not to migrate them to the Cloud. The architecture and design of these applications vary. Some of them are monolithic that maybe running on legacy hardware or on a mainframe. Other web based or client-server applications have a distributed architecture. These applications maybe interdependent on each other, and may have dependencies on external systems and data stores such as distributed applications with dependencies on information residing on the mainframe. Applications that are regulated must comply to certain government rules (e.g. their data must reside within the EU boundaries and can only be accessible from a private network) and must meet certain SLAs. The IT department has to factor in all these requirements to properly plan their Cloud migration strategy in order to identify candidate applications suited to be migrated to either public, private, or local Clouds.
Planning: Planning for the Cloud migration strategy is not an easy task requiring lots of preparations ahead of time. The migration strategy has to account for the impact on the organizational cultural changes, staffing, securing the funding and sponsorship. In addition to planning the logistics for the migration, the Cloud migration strategy should account for all the factors I previously discussed such as performance, required resources, timeline, risk mitigation, recovery plans, regulatory compliance, security & privacy, SLAs, business impact, risks and all other constraints. A detailed plan is needed to document all related activities required to migrate the applications.
Risk: Risk is an encompassing term in the context of a Cloud migration strategy. I mentioned earlier some of the issues and concerns corporate IT will be facing and how the responsibility of IT security will shift to the Cloud provider. Furthermore, there are potential issues with corporations meeting their SLAs since they no longer have full control of the PaaS performance, stability and availability. As an example, if a corporation has an SLA with their customers. If due to unforeseen reason, the PaaS platform is not performing or simply not available. The question is who will bare the responsibility to absorb the penalties for not meeting the SLA terms and conditions? the corporation or the Cloud provider? What about if there was a breach resulting in either a loss of data or data privacy?
Financial: There is, of course, a cost for migrating to the Cloud that should be compared to the current cost for running a data center. Software cost, licensing & renewals, operating cost, software maintenance, Cloud provider pricing model and others are all variables that should be factored in when performing the financial analysis. The results of the analysis should provide the organization a better understanding of the opportunity cost of their decision on whether or not to migrate to the Cloud.
In this post, I discussed six key factors for organizations to consider as part of the trade-off analysis when formulating their Cloud migration strategy.
For additional reading, you maybe interested in this paper “Cloud Migration: A Case Study of Migration an Enterprise IT System to IaaS“.
About the Author
 Sami Joueidi holds a Masters degree in Electrical Engineering and an Enterprise Architecture certification from Carnegie Mellon. He has over 20 years of experience as a technical leader of complex IT projects for Fortune 500 firms, in diverse roles such as Systems Integrator, DevOps, Cloud Architecture, Enterprise Architecture and Software Development & Release Management. He guides customers on how to leverage the latest technology trends to their advantage and helps them with their Cloud adoption strategies.
Sami Joueidi holds a Masters degree in Electrical Engineering and an Enterprise Architecture certification from Carnegie Mellon. He has over 20 years of experience as a technical leader of complex IT projects for Fortune 500 firms, in diverse roles such as Systems Integrator, DevOps, Cloud Architecture, Enterprise Architecture and Software Development & Release Management. He guides customers on how to leverage the latest technology trends to their advantage and helps them with their Cloud adoption strategies.
© Sami Joueidi and www.cafesami.com, 2015. Excerpts and links may be used, provided that full and clear credit is given to Sami Joueidi and www.cafesami.com with appropriate and specific direction to the original content.

Do you like to comment?